Read Next
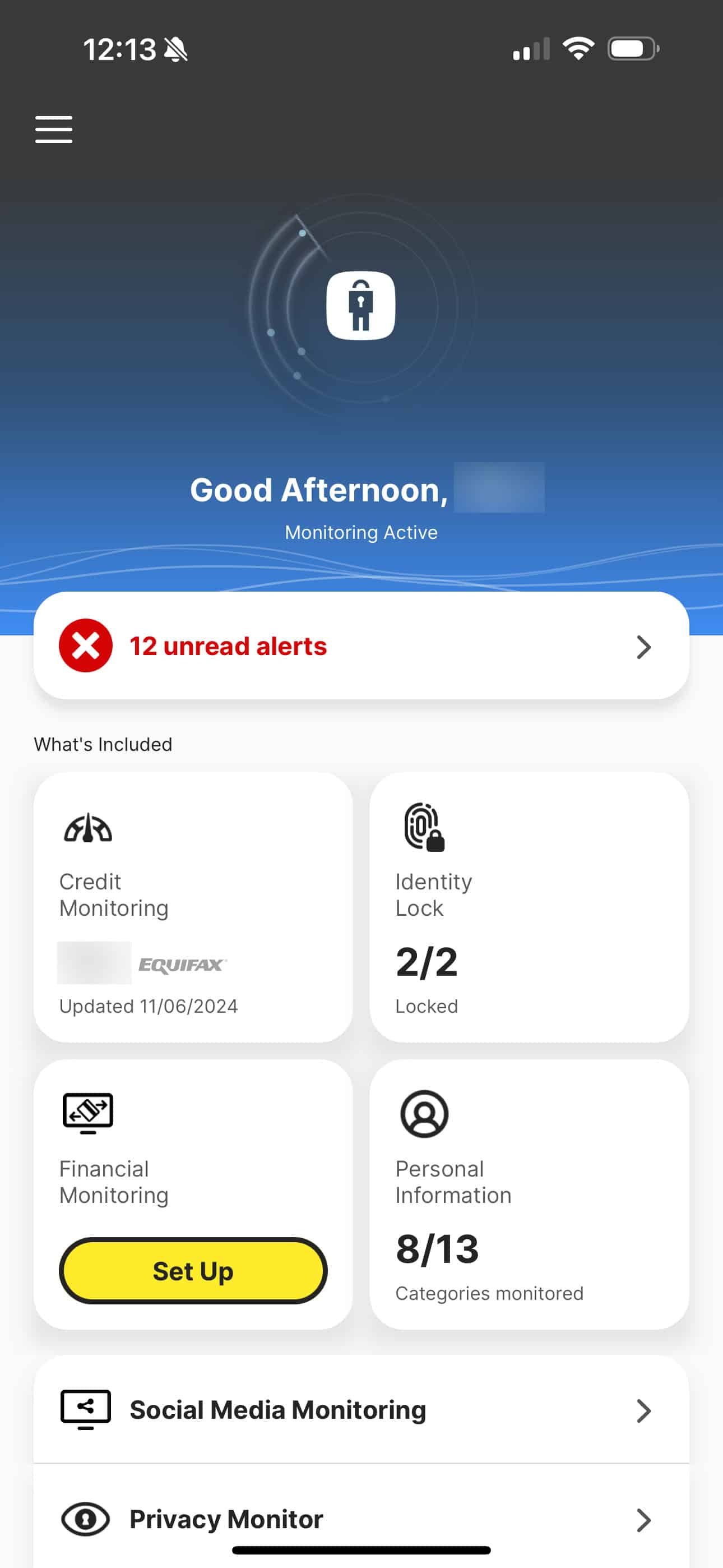
The Best Strategy To Use For Identity Protection Tools
Once they have methods to contact you, someone might send you a counterfeit message about suspicious activity in your...
Published Feb 12, 26
5 min read
More Posts
Navigation
Home
Latest Posts
The Best Strategy To Use For Identity Protection Tools
Published Feb 12, 26
5 min read
Getting My Identity Protection Tools To Work
Published Jan 29, 26
5 min read
Identity Protection Tools Fundamentals Explained
Published Jan 28, 26
5 min read